Blog
Thoughts on security, development, and blockchain.
Web3 security and OPSEC checklist: beyond the smart contract audit
A practical threat model for a small web3 company. Smart contract audits are just the start - here's everything else that can go wrong.

Hello Noir! [Part 2]
Using Barretenberg to generate and verify proofs, deploying a Solidity verifier with Foundry, and understanding the trust model.
Hello Noir! [Part 1]
Setting up the environment and getting an idea what and how will be used.
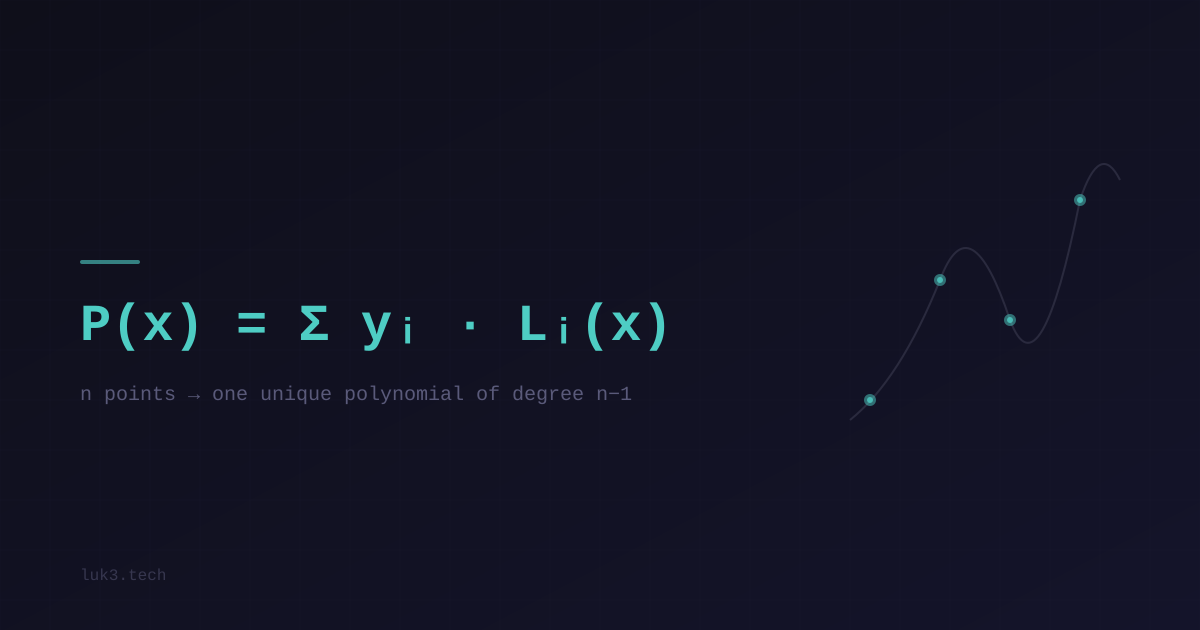
Lagrange interpolation: turning points into a polynomial
You have a list of points. Lagrange interpolation gives you the one polynomial that passes through all of them. Here's why ZK proofs care.
The Fiat-Shamir transform: how a hash function replaces a conversation
Schnorr signatures started as a back-and-forth conversation. Fiat-Shamir turned that conversation into a one-liner. Here's how a hash function replaces a trusted stranger.

Digital signatures: Schnorr, ECDSA and how PS3 was hacked
You made it through elliptic curves. Now let's see how they're actually used - signing things, proving identity, and why reusing a nonce will ruin your life.
